Information System Security Manager (ISSM) – Cloud Security Architect

509 jobs found — updated daily




















AETC recruits, trains, and educates Airmen to deliver 21st‑century airpower. AWAKEN is AETC’s enterprise‑managed, accredited wireless/network service spanning flight lines, classrooms, dorms, and administrative facilities across the U.S. As ISSM – Senior Cloud Security Architect, you will lead cybersecurity for AWAKEN’s cloud‑native, software‑defined, Zero‑Trust transformation, ensuring secure, reliable connectivity that advances the training mission at scale. This role is ideal for a hands‑on cloud security engineer first, policy‑aware second. You will actively engineer and enforce security controls across cloud and hybrid environments while maintaining RMF/ATO governance, continuous monitoring, and compliance. Expect roughly 66% platform engineering (secure design/implementation, automation, remediation) and 33% governance/policy enforcement (RMF artifacts, POA&Ms, attestations, board cadence).
Stand Out From the Crowd
Upload your resume and get instant feedback on how well it matches this job.
Job Type
Full-time
Career Level
Senior
Education Level
No Education Listed
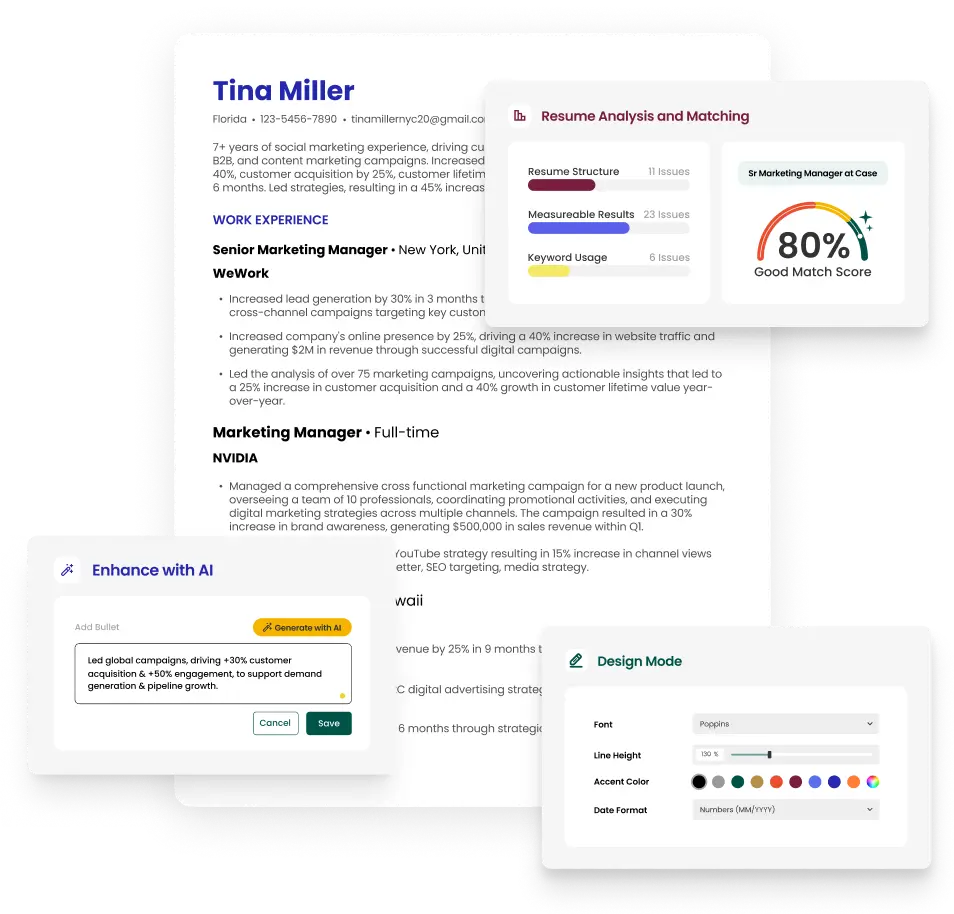
The resume builder that gets results.
Common questions about Security Architect careers and jobs.