Insider Threat Senior Analyst

77 jobs found — updated daily




















Our Cyber Threat Management team rolls up into Key’s broader Cyber Defense function within Corporate Information Security. Cyber Defense’s mission is simple: We aim to Deter, Detect, Deny, and Disrupt adversaries through proactive threat-centric defense. The Senior Insider Threat and Threat Hunting Analyst is a key member of the Cyber Threat Management (CTM) team. This role has responsibilities across both Insider Threat and Threat Hunting functions, with a primary focus on Insider Threat and a secondary focus on Threat Hunting. In this role, you will perform hands‑on technical analysis related to insider threat investigations and proactive threat hunting activities. You will also play a critical role in maturing both programs by assessing current capabilities, identifying potential enhancements, and recommending improvements to processes, tools, and detection strategies. This position blends deep technical execution with strategic program development to strengthen KeyBank’s overall threat posture. You will develop and maintain a deep understanding of the insider threat and cyber threat landscapes, by utilizing threat intelligence related to insider threats, along with threat actor Tactics, Techniques and Procedures (TTPs), and their associated threats, to support mitigation efforts while leveraging frameworks such as MITRE ATT&CK. This position requires strong insider threat and threat hunting investigation skills, and advanced knowledge of cybersecurity fundamentals and concepts. Success in this role demands an independent, thorough, and adaptable individual who can deliver accurate and complete intelligence outputs.
Stand Out From the Crowd
Upload your resume and get instant feedback on how well it matches this job.
Job Type
Full-time
Career Level
Senior
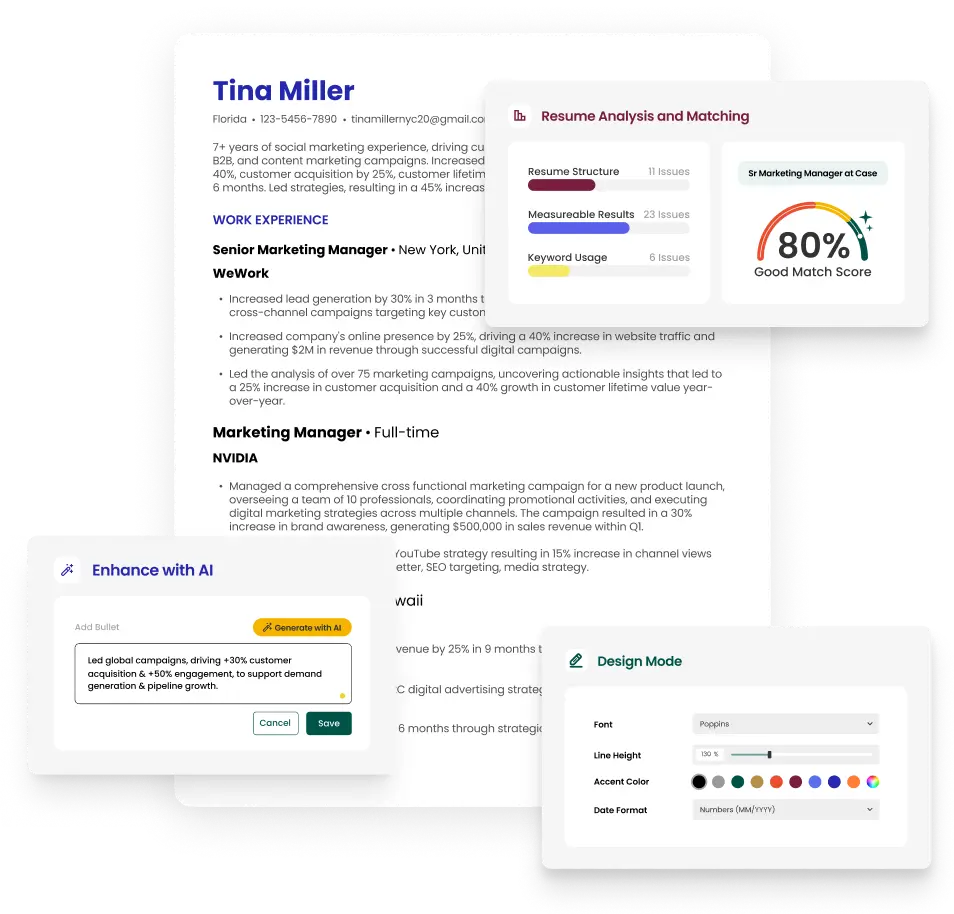
The resume builder that gets results.
Common questions about Forensic Analyst careers and jobs.